Recently I came across a need to create and assign multiple phone numbers and Resource Accounts to an Auto Attendant in Teams. To do this manually, the normal procedure is:
- Purchase the Phone System Virtual User licenses (FoC) via Microsoft or your CSP
- Go to Teams Admin Centre (TAC)
- Create the Resource Accounts
- Associate them with an Auto Attendant or Call Queue, one by one
- Go to Office 365 Admin Centre
- Set Usage Location (country) and assign Virtual User license to each of the Resource Accounts
- Go back to TAC (or use PowerShell) to assign a phone number to the Resource Accounts
It is not too bad if you only need to do that on a small number of Resource Accounts, but my recent encounter required me to associate 65 phone numbers to an Auto Attenant. The above manual steps would be end of my will to live.
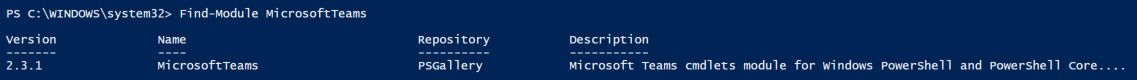
So, I created a PowerShell script to do such task for me!
The script can carry out the above actions based on a CSV import.
You can choose to have the script to do all of it, or only some of it by skipping certain steps.
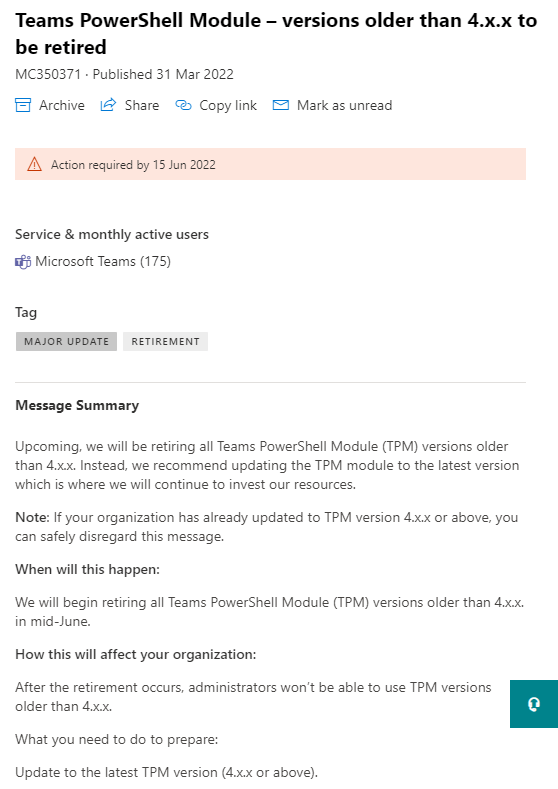
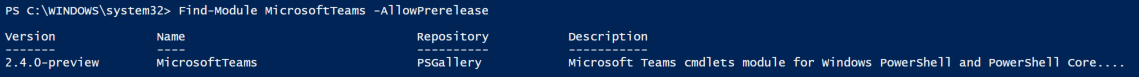
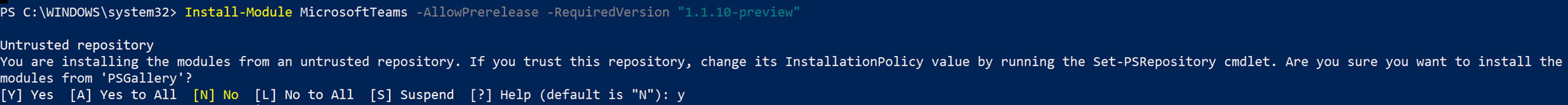
The script can’t do EVERYTHING EVERYTHING. So, there are certain things need to be in place before hand – you would most likely need to have them anyway.
The CSV file only need a few details for each Resource Account. It is rather self-explanatory. The only note is: populate the phone numbers without the leading + sign.
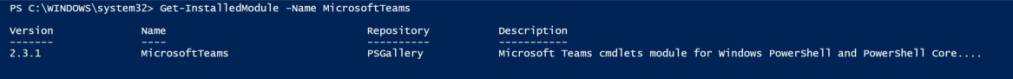
You can use any CSV editor you’d prefer. Excel sometimes try to be too clever for its own good by applying formatting to the phone numbers automatically. So, watch out for that.
To correct it, you need to set the cell to Number and get rid of the decimal points.
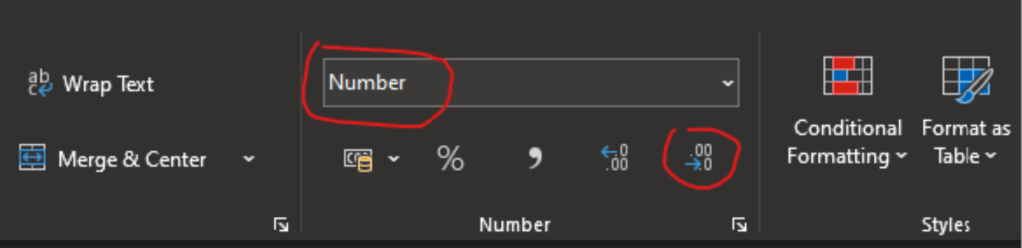
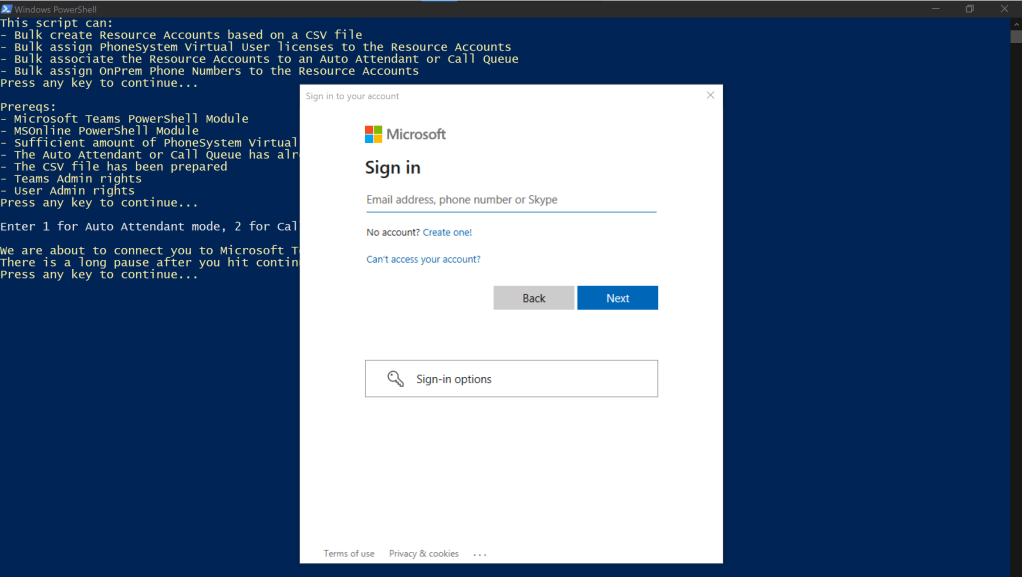
The script will start by asking you to set it to either Auto Attendant or Call Queue mode. This will set the tone for the rest of the script.
It will then give you a heads up to have your access credentials at hand.
After choosing to proceed, you will see the familar login pop-up.
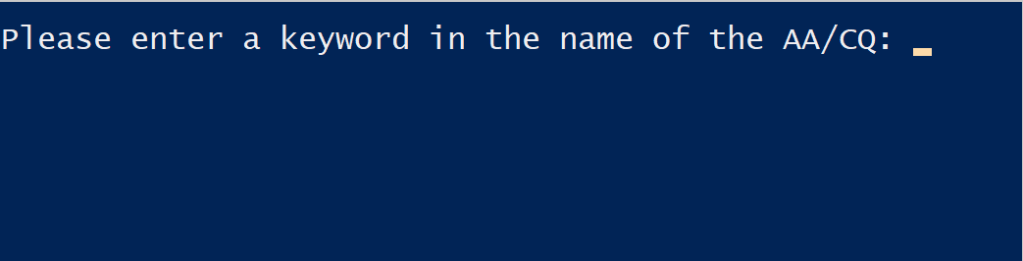
After successful authentication, the script will ask you for a AA/CQ search string.
You don’t have to enter the full name of the AA/CQ. A partial name or a keyword would be sufficient for the script to run a search. It will return the search result and ask you for confirmation before proceeding further. If the returned the result isn’t the AA/CQ you are looking for, you can enter N to enter a new keyword to search.
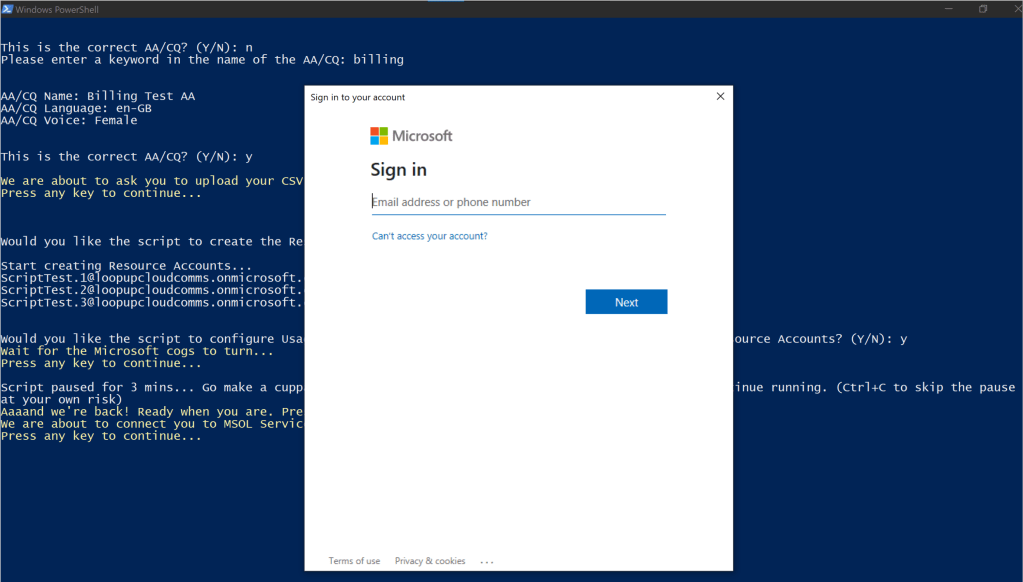
Next up, is the CSV import. The script will pause and give you a heads up before prompting for the file.
Now the script will start the actual job at hand.
Creating the Resource Accounts
The script will first ask for your confirmation. You can enter N to skip this step of the script.
If you chose Y to proceed, the script will carry on to create the Resource Accounts listed in the CSV file.
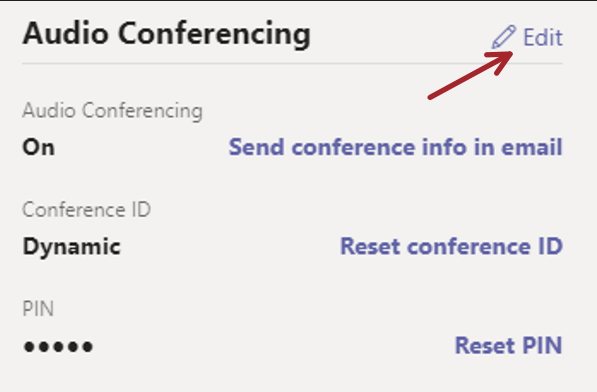
Configuring Usage Location and assign Phone System Virtual User license
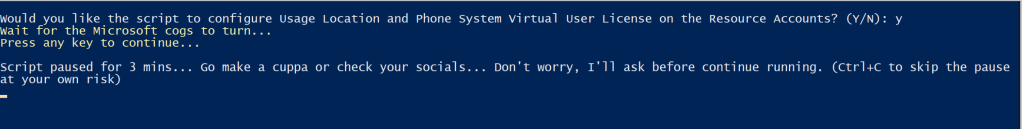
Same as above, the script will ask for your confirmation. You can enter N to skip this task if you wish to.
The reason these 2 steps are combined together is that although the Usage Location is not required when you create the Resource Account, it is mandatory when you assign the Virtual User license to it.
Once you have given permission, the script will proceed to perform the tasks. As you know, sometimes there could be a provisioning delay in Microsoft cloud. This could cause the script to error out and complain that the user accounts cannot be found. So, I have built a 3-minute pause into the script to avoid errors.
The script will promp you once the timer is up. Of course, you can leave it for longer if you wish to. (e.g. If you have a large amount of the accounts in the CSV list)
To proceed at this step, you’ll need to enter your credentials to authenticate against MSOnline service.
Once authenticated, the script will proceed to do its thing.
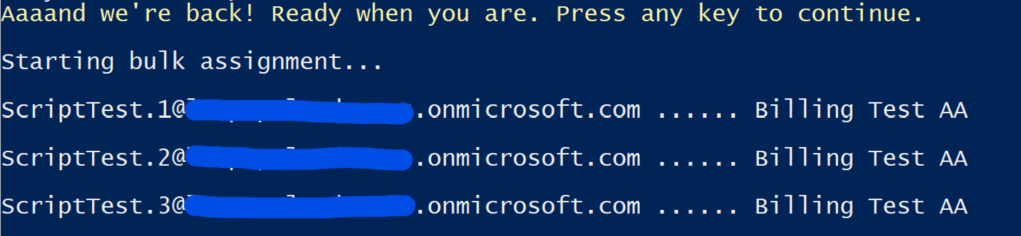
Associate the Resource Accounts to the Auto Attendant or Call Queue
Same as previously, you have to choice to say yay or nay. The script will skip this step if you don’t want it to do it.
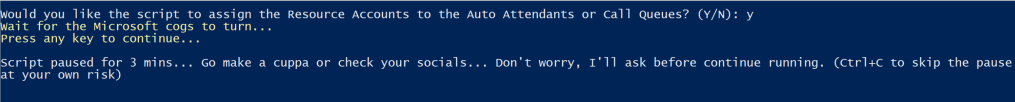
As as before, there is built-in 3-minute pause here to avoid any provisioning delay that could cause the script to error out.
The script will prompt you to continue after the 3-minute timer.
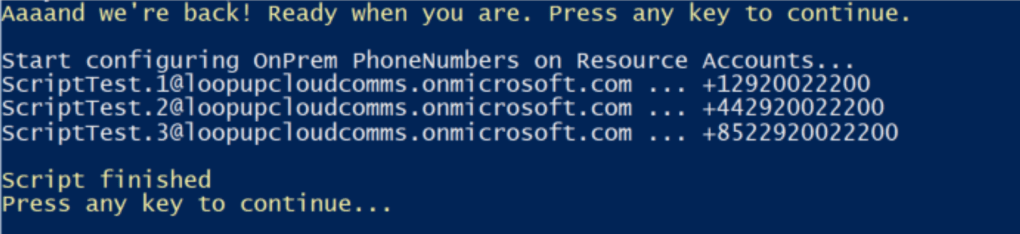
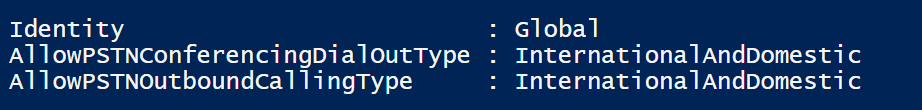
Assign OnPrem Phone Numbers to the Resource Accounts
You guessed it, you get to choose whether or not you want the script to do this part by entering Y or N.
And, yes, there is another 3-minute timer to avoid errors caused by provisioning delays at Microsoft’s end.
This is the last task for the script to carry out before it completes.
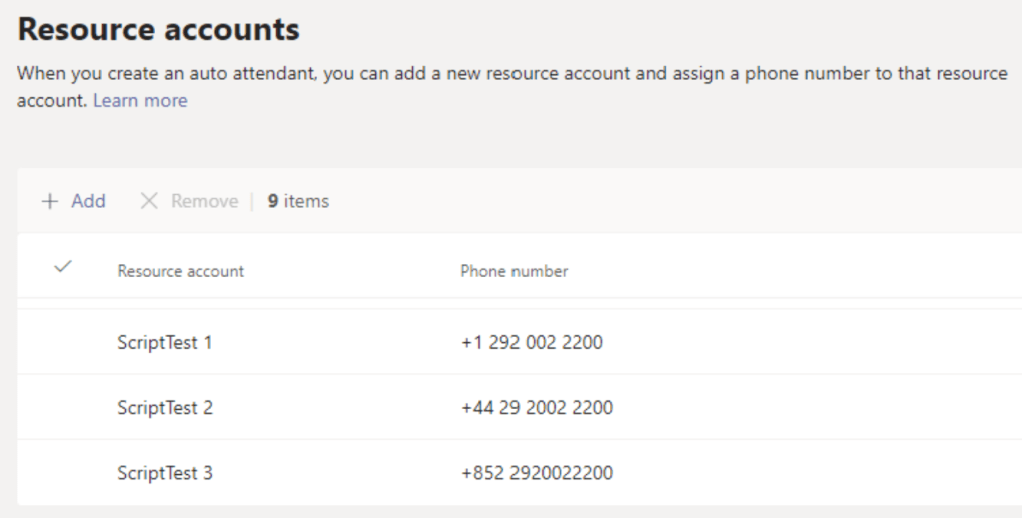
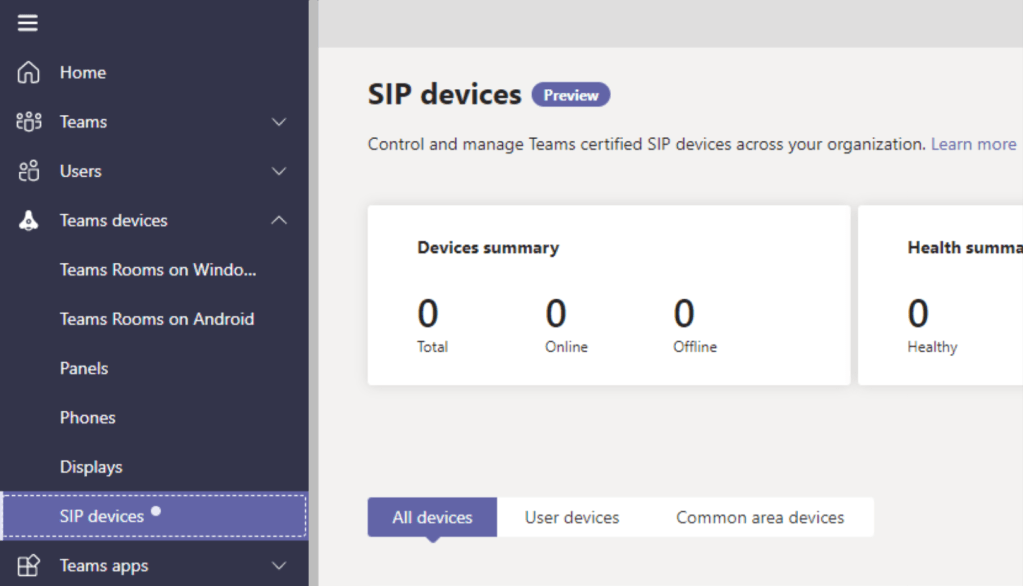
If you wish to, you can double check the assignment result in the TAC GUI.
Now the actually goodies. You can download the script and the CSV file example from here.
I hope this script can be helpful to you.